Constructing on the rising physique of labor on the menace posed by North Korea’s (Democratic Folks’s Republic of Korea or DPRK) IT workforce, the Multilateral Sanctions Monitoring Group (MSMT), an 11-nation consortium monitoring sanctions violations and evasions, not too long ago revealed an in depth report on DPRK’s use of cyber operations and IT labor actions to bypass UN sanctions.
Constructing on the rising physique of labor on the menace posed by North Korea’s (Democratic Folks’s Republic of Korea or DPRK) IT workforce, the Multilateral Sanctions Monitoring Group (MSMT), an 11-nation consortium monitoring sanctions violations and evasions, not too long ago revealed an in depth report on DPRK’s use of cyber operations and IT labor actions to bypass UN sanctions.
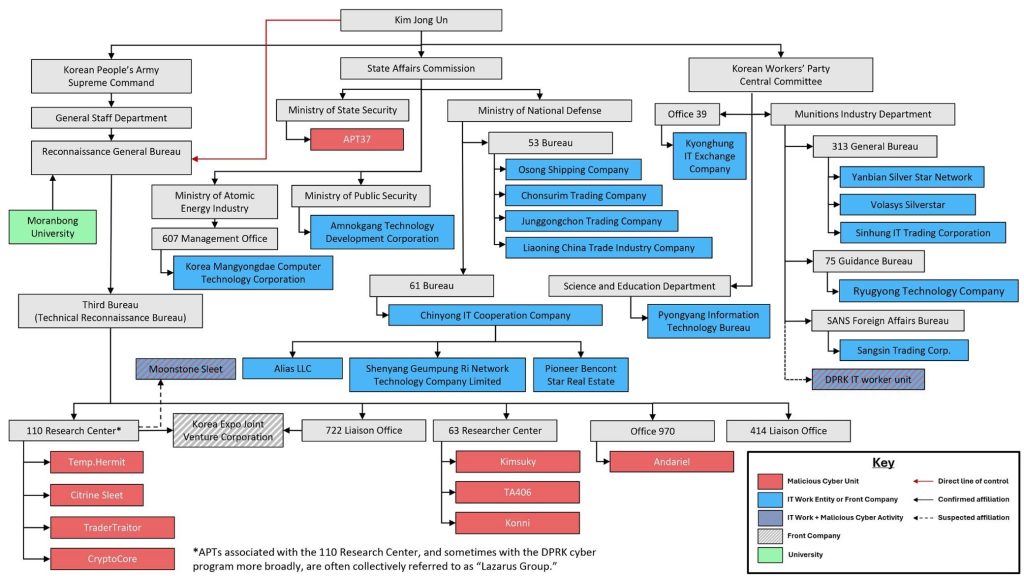
Drawing on insights from member state submissions, private-sector intelligence and open-source assets, the report presents one of the crucial complete overviews of the DPRK’s cyber ecosystem. From mapping the technical infrastructure, international hiring patterns, widespread Ways, Methods and Procedures (TTPs), cryptocurrency laundering mechanisms and the operational overlaps between cyber models and IT groups linked to UN designated entities.
Nevertheless, a key takeaway from the report emerges from this very overlap. The report locations the IT employee difficulty throughout the broader paradigm of DPRK cyber operations, slightly than a definite and self-sustaining financial exercise. This framing, whereas comprehensible, dangers masking the monetary reasoning and organizational construction that make IT employee operations uniquely persistent but in addition each a malicious menace vector and a strategic revenue-generation enterprise mannequin.
Distinctive Takeaways on IT Employees
First, the report’s examination of the organizational preparations together with the potential hierarchy and division of labor throughout state, get together and army entities, affords a structured framework. This helps reconcile the amount of data scattered throughout open-source investigations, private-sector reviews, and successive UN Panel of Consultants reviews. It additionally contextualises the IT employee equipment inside this broader bureaucratic equipment designated by UN sanctions. Moreover, identification of front-company constructions and named entities clarifies the place IT staff sit inside this ecosystem and the way their output contributes to revenue-generation.
Second, the report offers a extra concrete sense of the dimensions of DPRK IT employee operations and the income they generate. Past the broad earnings ranges cited in authorities advisories, the MSMT estimates that staff usually earn between $3,500 and $10,000 per thirty days, with excessive performers incomes considerably extra.
A very vital contribution is its documentation of instances, supported by private-sector attributions, demonstrating that some IT staff have performed direct operational roles in cryptocurrency thefts. That is inclusive of the possible function within the Munchables incident in 2024, the Onyx DAO exploit and the BTCTurk breach. This challenges the present view that the features of DPRK IT staff are restricted to software program growth or freelance IT work. As an alternative, it highlights the twin nature of their actions involving each malicious and revenue-generation components.
Third, the report offers detailed case research of entrance firms together with their company constructions, bodily places, and operational features. These instances present the range of DPRK IT employee placements, spanning healthcare methods, on-line playing platforms, animation studios, and blockchain-related providers. Accompanying this evaluation of abroad IT staff is an examination of home IT amenities located in Rason (Rajin-Sonbong), Sinuiju, and Pyongyang. This info suggests the existence of coaching hubs and operational centres that probably coordinate abroad deployments and handle income flows.
Fourth, the report offers a breakdown of IT employee TTPs. It categorizes IT employee exercise into three operational phases: 1) establishing a persona, together with identification laundering, credential fabrication, and the procurement of freelancer accounts; 2) making use of for work, leveraging brokers, compromised HR accounts, and focused purposes to industries with weak onboarding controls; and three) receiving and exfiltrating funds by way of cost processors, crypto rails, mixing providers and over-the-counter (OTC) brokers. Whereas these TTPs have been documented earlier than, the MSMT’s structured rationalization consolidates distinct indicators right into a coherent operational mannequin. Thus, making it simpler for governments, cost platforms, and monetary establishments to determine and interdict DPRK IT employee exercise.
The place the Report Falls Brief
One main shortcoming of the report is its remedy of DPRK IT staff as a part of the bigger DPRK cyber ecosystem. By viewing IT staff as an extension of malicious cyber exercise, the report blurs necessary distinctions between the monetary, organizational, and operational points that govern their deployment. This method might conflate two associated however typically distinct ecosystems, together with these concerned in malicious acts and people targeted on revenue-generation.
The report acknowledges that IT employee income is routed again to mum or dad entities concerned in weapons growth, manufacturing, home infrastructure initiatives, and consumer-goods procurement. Nevertheless, it stops wanting explicitly addressing whether or not income technology is the first mission of those IT staff or whether or not they more and more serve a hybrid function mixing IT work with opportunistic malicious exercise.
The Munchables incident illustrates this ambiguity. The MSMT notes that the people concerned had been probably IT staff who exploited sensible contracts within the Non-Fungible Tokens (NFT) sport Munchables, stealing 17,413.96 Ethereum (valued at $62.5 million on the time). Nevertheless, the next operational failures spotlight their limitations as they struggled to maneuver the stolen belongings off the Blast community and demonstrated little proficiency in laundering or obfuscating funds. Their ability set aligned extra with smart-contract growth than with on-chain obfuscation typical of subtle cyber menace models. This implies a extra advanced ecosystem by which IT staff might interact in financially motivated cybercrime, however not essentially with the identical intent or technical competency as designated DPRK cyber models.
Including to this complexity is the report’s temporary acknowledgement that malicious cyber operators typically collaborate with IT employee groups. Nevertheless, it stops wanting highlighting how these collaborations are structured, whether or not they’re advert hoc or systematic, or how such partnerships reshape the danger profile of distant IT staff. That is notably related given the rising variety of authorities advisories warning that DPRK IT staff pose not solely sanctions evasion dangers but in addition insider-threat, extortion, and data-theft dangers to employers.
A second space the place the report falls brief is in its remedy of monetary community of IT staff. Whereas the TTPs present a transparent depiction of how DPRK IT staff fabricate identities and safe distant roles, the knowledge supporting IT employee laundering methodology is extra scattered and non-cohesive when inspecting how funds are acquired, moved, and finally consolidated.
To its credit score, the report does provide intensive case research. For instance, the report notes IT staff stationed abroad counting on third-party purchases of PayPal USD (PYUSD), incremental conversions into USDT/USDC underneath day by day limits, and acquisition of fraudulently obtained automated clearing home (ACH)-enabled financial institution accounts by way of facilitators. The report additionally notes that some IT employee groups have begun establishing shell firms together with US registered entities to obtain funds instantly, whereas one other case particulars a DPRK official utilizing China UnionPay playing cards tied to Chinese language banks to conduct transactions on behalf of staff, together with for a China-based entity, 313 Basic Bureau IT employee. This hole is additional notable because the report paperwork instances of IT employee monetary operations in jurisdictions as various as China, Russia, the UAE, Pakistan, Argentina, Ukraine, Vietnam, the US, and Japan.
Briefly, the report offers an in depth stock of laundering methods that exhibit the evolution of its tradecraft. Nevertheless, they don’t quantity to a scientific mapping of how these components join right into a coherent monetary community as they current remoted behaviours. With out establishing these linkages, it’s troublesome to find out which nodes are most exploited, which intermediaries are fungible, and the place the system is most susceptible to disruption. Policymakers are left with snapshots of illicit transactions slightly than an understanding of the structural flows that maintain DPRK IT employee operations. Thus, making it troublesome to design enforcement actions able to mitigating it at scale.
A last shortcoming pertains to the sensible utility of the report. The influence of the MSMT’s findings hinges on how successfully governments, platforms, and monetary establishments can operationalize the findings. Whereas the report offers clear descriptions of DPRK’s cryptocurrency-laundering strategies, it doesn’t totally clarify IT staff’ roles in these processes or prioritise the riskiest nodes throughout the community. In impact, the usefulness of the MSMT’s work relies upon closely on the analytical capability of its reader to sew collectively disparate case research, join it with nationwide advisories and suggestions prompt together with designing enforcement mechanisms. This locations an unreasonable burden on already resource-constrained jurisdictions and will increase the probability that the findings are erratically utilized, partially applied, and even misinterpreted in ways in which would possibly slender the coverage response.
Conclusion
The MSMT report is, with out query, one of the crucial detailed assessments of DPRK’s cyber operations and its IT employee equipment. It brings collectively insights that a number of open-source investigations and private-sector reviews have solely captured in fragments, and it considerably strengthens the evidentiary base for policymakers, compliance groups, and researchers.
However the report’s worth is formed by its limitations. Its gaps, notably across the monetary networks sustaining IT employee operations and the blurred strains between cyber models and revenue-generation groups, instantly affect the utility of its findings. These shortcomings don’t diminish the report’s contribution, however they do spotlight the place extra work is required.
That is the place civil society, investigative researchers, and compliance specialists can play a key function. Organizations with deep familiarity in DPRK’s cyber, procurement, and illicit-finance ecosystems are effectively positioned to bridge the divide between detailed case research and the system-level maps wanted for efficient countermeasures. They’ll translate the MSMT’s findings into sensible steerage, focused outreach, and capacity-building for the jurisdictions and establishments most uncovered to those dangers.
If the MSMT report is to succeed in its full potential, it would require exact follow-up evaluation work carried out by civil society establishments to determine the blind spots in organizational controls, strengthen sanctions compliance, and assist mitigate the very vulnerabilities that allow DPRK IT employee operations to thrive.